Choose from a wide range of NEWCV resume templates and customize your NEWCV design with a single click.
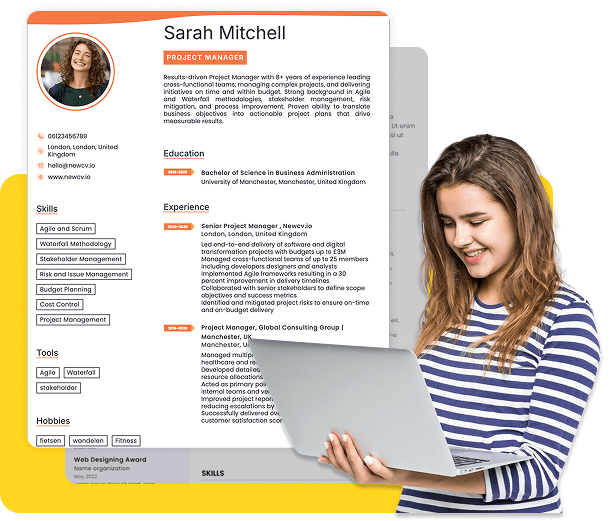
Use ATS-optimised Resume and resume templates that pass applicant tracking systems. Our Resume builder helps recruiters read, scan, and shortlist your Resume faster.


Use professional field-tested resume templates that follow the exact Resume rules employers look for.
Create Resume

Use professional field-tested resume templates that follow the exact Resume rules employers look for.
Create ResumeCybersecurity hiring is one of the most competitive and misunderstood segments of the job market.
Everyone has certifications. Everyone lists tools. Everyone claims “security expertise.”
Yet most resumes fail.
Not because of lack of knowledge—but because they don’t communicate real security value in a way that aligns with how hiring decisions are made.
AI resume builders can help you structure and optimize your resume—but if used incorrectly, they will make you blend in with thousands of other candidates.
This guide shows you how to use AI resume builders specifically for cybersecurity roles—based on how resumes are actually evaluated by ATS systems, recruiters, and security hiring managers.
Cybersecurity is not a generic field.
It is:
Risk-driven
Evidence-based
Highly contextual
Outcome-focused
Recruiters and hiring managers are not looking for:
“Someone who knows tools”
They are looking for:
“Someone who can reduce risk, detect threats, and respond effectively”
That distinction is where most AI-generated resumes fail.
Cybersecurity ATS filters look for:
Specific tools (SIEM, Splunk, Wireshark)
Certifications (Security+, CEH, CISSP)
Keywords (threat detection, incident response, vulnerability management)
If these are missing, your resume never gets seen.
Recruiters are not deeply technical.
They look for:
Recognizable tools
Clear role alignment (SOC Analyst, Security Engineer)
Clean, structured resumes
They reject:
Overly technical jargon with no clarity
Generic “security enthusiast” profiles
This is where decisions are made.
Security leaders look for:
Real-world application
Understanding of threats and risks
Evidence of problem-solving
They ask:
“Can this person actually handle a security incident?”
AI outputs:
Long lists of tools
No explanation of usage
Result:
Looks like keyword stuffing, not expertise.
AI writes:
“Worked with SIEM tools”
But doesn’t explain:
What threat was detected
What action was taken
What impact it had
Cybersecurity is about:
Prevention
Detection
Mitigation
If your resume doesn’t show impact, it fails.
Cybersecurity is not one job.
You must choose a lane:
SOC Analyst
Security Engineer
Penetration Tester
GRC Analyst
AI needs this context to generate relevant content.
Instead of:
“I used Wireshark”
Write:
“Analyzed network traffic using Wireshark to identify suspicious patterns and potential intrusion attempts”
Now AI can enhance meaningful content.
Prompt AI with:
“Add measurable impact”
“Show threat detection and mitigation”
“Frame this as incident response experience”
AI cannot fully simulate:
Attack scenarios
Security reasoning
Trade-offs
You must refine this yourself.
This is your identity.
Weak Example:
“Cybersecurity enthusiast with knowledge of security tools”
Good Example:
“Detail-oriented Cybersecurity Analyst with hands-on experience in threat detection, network monitoring, and incident response through lab environments and real-world simulations. Skilled in SIEM tools, log analysis, and vulnerability assessment, with a proven ability to identify and mitigate potential security risks.”
What changed:
Specific focus
Practical exposure
Security outcomes
Organize like this:
Security Tools: Splunk, Wireshark, Nessus
Technical Skills: Network Security, Threat Analysis, Incident Response
Frameworks: NIST, ISO 27001
This improves:
ATS performance
Recruiter readability
This is where hiring decisions happen.
Threat context
Action taken
Result or outcome
Weak Example:
“Performed vulnerability scanning”
Good Example:
“Conducted vulnerability assessments using Nessus, identifying critical system weaknesses and recommending remediation strategies that reduced exposure risk in simulated environments”
Cybersecurity hiring heavily values certifications.
Include:
CompTIA Security+
CEH
CISSP (if applicable)
But remember:
Certifications get attention, not offers.
Include naturally:
Threat Detection
Incident Response
Vulnerability Management
SIEM
Network Security
Use standard headings
Avoid graphics or tables
Keep it machine-readable
If you lack experience, create it:
Home labs
Capture The Flag (CTF) challenges
Simulated attacks
Then describe them like real work.
Paste job description into AI and ask:
“What are the top skills required?”
“What responsibilities are expected?”
Then align your resume.
Your resume must tell one story:
“I am a cybersecurity professional who can reduce risk”
Not:
“I know many tools”
Result: Looks like keyword stuffing
Result: Signals theoretical knowledge only
Result: No proof of real capability
Result: Recruiters reject due to confusion
Result: Immediate rejection
From real cybersecurity hiring behavior:
Hands-on labs and simulations
Clear understanding of threats
Action + outcome-based bullet points
Role-specific positioning
“Cybersecurity enthusiast” with no proof
No mention of real scenarios
Tool-heavy, impact-light resumes
Candidate Name: Daniel Mehta
Target Role: SOC Analyst
Location: London, UK
PROFESSIONAL SUMMARY
Cybersecurity Analyst with hands-on experience in threat detection, network monitoring, and incident response through lab environments and simulated attack scenarios. Skilled in SIEM tools, log analysis, and vulnerability management, with a proven ability to identify security threats and recommend mitigation strategies.
SKILLS
Security Tools: Splunk, Wireshark, Nessus
Technical Skills: Network Security, Threat Detection, Incident Response
Frameworks: NIST, ISO 27001
PROJECT EXPERIENCE
Network Traffic Analysis Lab
Monitored network traffic using Wireshark to identify suspicious patterns and potential intrusion attempts
Analyzed packet data to detect anomalies and recommend security improvements
Vulnerability Assessment Project
Conducted vulnerability scans using Nessus
Identified critical vulnerabilities and proposed remediation strategies to reduce risk exposure
SIEM Log Analysis Simulation
Used Splunk to analyze security logs and detect potential threats
Created alerts for unusual activity patterns, improving detection efficiency in simulated environments
CERTIFICATIONS
CompTIA Security+
EDUCATION
Bachelor of Science in Information Technology
ABC University
Cybersecurity keyword optimization
Role-specific templates
Bullet point enhancement
ATS compatibility
Focus only on design
Generate generic content
Lack customization
AI is making resumes easier to create.
But that means:
More competition
Less differentiation
Higher expectations
The winning candidates:
Use AI as a tool
Apply human strategy
Show real capability
Keywords
Structure
Context
Impact
Clarity