Choose from a wide range of NEWCV resume templates and customize your NEWCV design with a single click.
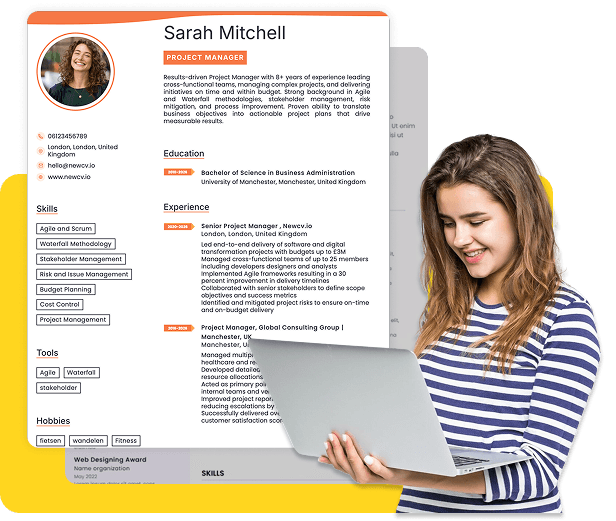
Use ATS-optimised Resume and resume templates that pass applicant tracking systems. Our Resume builder helps recruiters read, scan, and shortlist your Resume faster.


Use professional field-tested resume templates that follow the exact Resume rules employers look for.
Create Resume

Use professional field-tested resume templates that follow the exact Resume rules employers look for.
Create ResumeThe salary of an information security analyst is not just a number tied to a job title. It is a direct reflection of how the market values risk mitigation, technical depth, and business impact. If you understand how compensation is actually determined across ATS filters, recruiter pipelines, and hiring manager expectations, you can position yourself to earn significantly above the median.
This guide breaks down real salary ranges, what drives compensation at each level, and how elite candidates consistently command top-tier offers in cybersecurity.
In the US job market, the salary range for an information security analyst varies widely based on experience, specialization, and company type.
Base Salary Benchmarks (US Market):
Entry-level (0–2 years): $70,000 – $95,000
Mid-level (3–6 years): $95,000 – $130,000
Senior-level (7–12 years): $130,000 – $180,000
Lead / Principal: $160,000 – $210,000+
Total Compensation (Including Bonus + Equity):
Tech companies: $140,000 – $250,000+
Financial institutions: $120,000 – $220,000
Location still plays a major role, even in hybrid and remote environments.
Top Paying Cities:
San Francisco: $140,000 – $210,000
New York City: $130,000 – $200,000
Washington DC: $120,000 – $180,000
Austin: $110,000 – $170,000
Seattle: $130,000 – $190,000
Remote roles are increasingly leveling salaries, but top companies still anchor offers based on market tiers.
Recruiter Insight:
Candidates who apply nationally instead of locally often increase their offer range by 20% to 40% without changing their skill set.
Government / public sector: $85,000 – $140,000
The biggest mistake candidates make is benchmarking only base salary. Hiring managers often evaluate compensation holistically, especially in cybersecurity roles tied to business risk.
Typical offers depend heavily on certifications and internship experience.
Without certifications: $70K – $80K
With Security+ / CEH: $80K – $95K
What recruiters actually look for:
Hands-on labs or projects
Familiarity with SIEM tools
Exposure to incident response
Common mistake: Listing theoretical knowledge without proof of execution.
This is the most competitive salary band because candidates start differentiating.
Typical range: $95K – $130K
High performers: $130K – $150K
Key salary drivers:
Ownership of security incidents
Experience with compliance frameworks (NIST, ISO 27001)
Cloud security exposure
Hiring manager perspective:
At this level, candidates are evaluated on decision-making, not just execution.
Typical range: $130K – $180K
Top-tier candidates: $180K – $220K+
What separates top earners:
Leading security strategy
Reducing organizational risk
Influencing cross-functional teams
Hidden insight:
Technical skills alone do not drive senior salaries. Business alignment does.
Salary is not random. It follows clear evaluation signals across ATS, recruiters, and hiring managers.
The more financial or reputational risk you manage, the higher your salary.
Monitoring logs = lower pay
Preventing breaches = higher pay
Designing security architecture = premium pay
General analysts earn average salaries. Specialists earn significantly more.
High-paying specializations:
Cloud security (AWS, Azure)
Threat intelligence
Application security
Identity and access management
Not all certifications are equal.
High ROI certifications:
CISSP
CISM
AWS Security Specialty
Low impact (alone):
Recruiter reality:
Certifications only increase salary when paired with real-world application.
Different industries pay differently for the same role.
Tech: Highest pay, highest expectations
Finance: High pay, compliance-heavy
Healthcare: Moderate pay, high demand
Government: Lower pay, high stability
Recruiters spend 6 to 10 seconds scanning a resume. Salary expectations are inferred instantly.
They look for:
Scope of responsibility
Tools and technologies used
Quantifiable impact
Progression over time
Weak Example:
Responsible for monitoring security systems
Good Example:
Reduced incident response time by 35% through implementation of automated SIEM workflows
Why this matters:
Impact-based statements directly correlate with higher salary brackets.
ATS systems don’t determine salary, but they determine access to higher-paying roles.
Keywords that matter:
SIEM (Splunk, QRadar)
Incident response
Threat detection
Vulnerability management
Cloud security
Hidden insight:
Candidates missing critical keywords are filtered out of higher-paying roles before a human even sees their resume.
Top candidates don’t stay stagnant.
Switch companies every 2 to 3 years
Move into specialized roles
Target high-paying industries
Combine multiple high-value skills:
Security + Cloud
Security + DevOps
Security + Data
This multiplies your market value.
Most candidates leave money on the table.
What works:
Multiple offers
Market data
Demonstrated impact
Recruiter truth:
If you don’t negotiate, you typically lose 10% to 20% of potential salary.
Leads to salary stagnation
Reduces market competitiveness
Undervalues experience
Attracts lower salary offers
To fully understand this topic, users typically search for:
information security analyst salary entry level
cybersecurity analyst salary USA
how much do security analysts make
senior information security analyst salary
cybersecurity salary by experience
information security analyst salary per hour
highest paying cybersecurity jobs
These queries reflect deeper intent around growth, comparison, and strategy.
Hiring managers are not paying for tasks. They are paying for outcomes.
They prioritize:
Risk reduction
System resilience
Compliance success
Business continuity
If your resume does not clearly show these, you are automatically positioned in a lower salary bracket.
Candidate Name: Daniel Carter
Target Role: Senior Information Security Analyst
Location: New York, NY
PROFESSIONAL SUMMARY
Results-driven Information Security Analyst with 8+ years of experience securing enterprise environments, reducing cyber risk, and leading incident response initiatives. Proven track record of decreasing security incidents by 40% and strengthening compliance across cloud and on-prem systems.
CORE SKILLS
Threat Detection & Incident Response
SIEM (Splunk, IBM QRadar)
Cloud Security (AWS, Azure)
Vulnerability Management
NIST & ISO 27001 Compliance
Security Automation
PROFESSIONAL EXPERIENCE
Senior Information Security Analyst – FinTech Corp
New York, NY | 2021 – Present
Led incident response strategy, reducing breach impact risk by 45%
Implemented SIEM automation, cutting response time by 35%
Strengthened cloud security posture across AWS infrastructure
Collaborated with engineering teams to secure DevOps pipelines
Information Security Analyst – Tech Solutions Inc
Boston, MA | 2018 – 2021
Monitored and analyzed security events across enterprise systems
Conducted vulnerability assessments and remediation planning
Improved compliance adherence to NIST standards
EDUCATION
Bachelor’s Degree in Cybersecurity
CERTIFICATIONS
CISSP
AWS Certified Security Specialty
The difference between a $90K analyst and a $180K analyst is not just experience. It is positioning, impact, and strategic career decisions.
If you:
Show measurable impact
Specialize in high-value areas
Align with business outcomes
You will consistently earn at the top of the salary range.